PEAK CARES
CUSTOMER SUPPORT
Our Mission
To be the most employee and customer service centered Internet service provider in the industry. We offer ourselves as a resource to our community & provide quality Internet services that help customers achieve their goals through our drive for innovation, service, and reliability.
How does Fiber-To-The-Home work?
In the areas that PEAK Internet provides Fiber-to-the-Home, also known as PEAK Fiber, PEAK delivers a physical fiber connection to the home. It will be required for PEAK to install equipment in or on your home to enable this connection to work. Once Fiber has been installed into the home, customers will be capable of having the fastest internet speeds available.
How does Fixed Wireless work?
Fixed Wireless is a type of Internet service that relies on towers located on high points like hills and mountains within your area that we can then pick up with an antenna mounted to your home. We have a great diagram here which shows a visual representation of the basics of fixed wireless service.
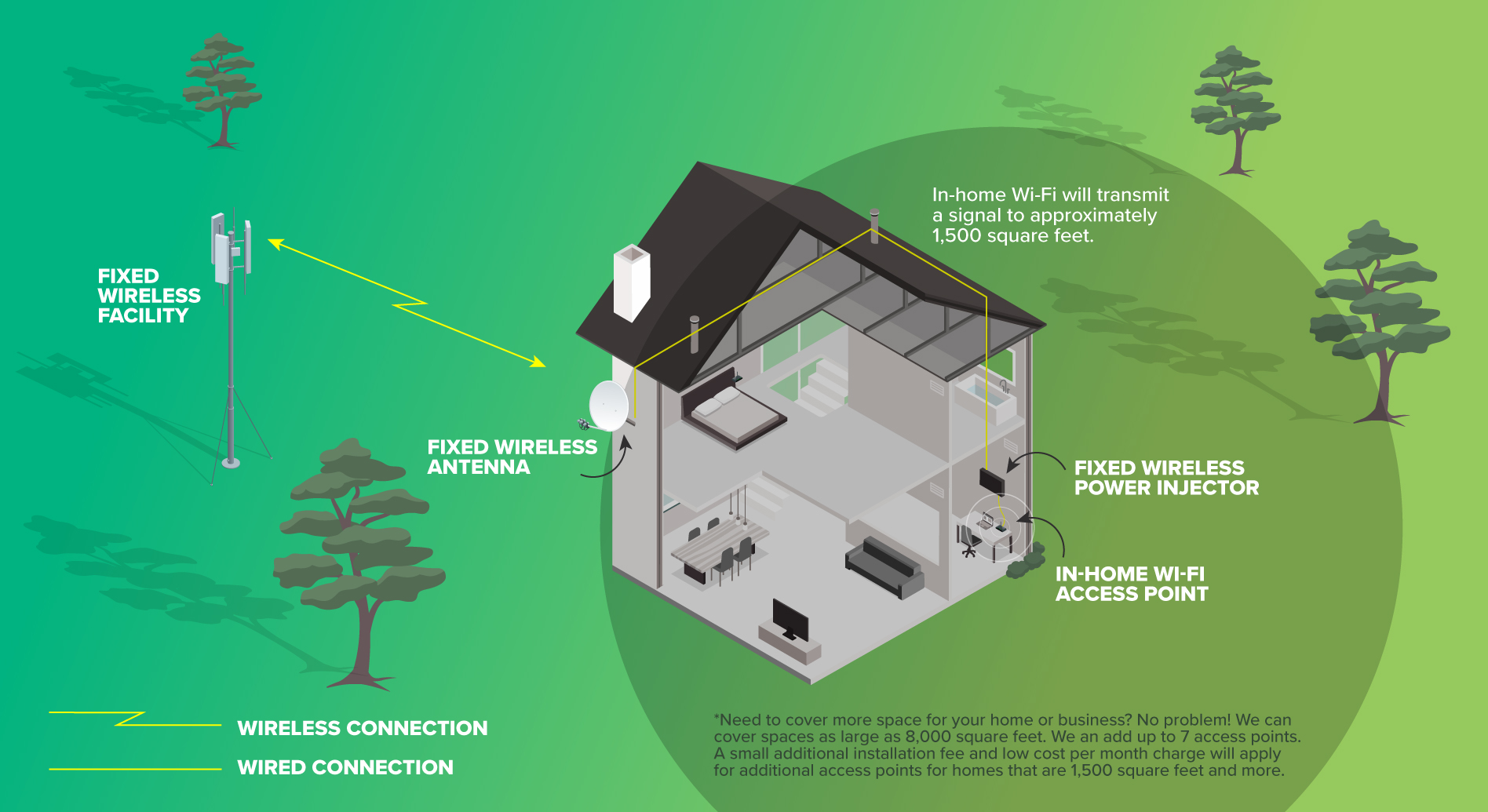
The great thing about this option is that we can offer Internet service to a large area without the need of a traditional cable or phone lines connecting your home.
What kind of plans are recommended for different household sizes?
The type of Internet plan that you choose is highly dependent on you and your families specific use. For the most part PEAK recommends that larger households subscribe to a higher speed tier.
When will I be able to receive Fiber-To-The-Home at my residence? (sub questions like why can’t I get Fiber to my home?)
In order for a customer to be connected to PEAK Fiber, PEAK must have fiber infrastructure in the area. PEAK has a very extensive network, with several areas that we offer PEAK Fiber. To see if your home qualifies use the Order Now tool to check availability. If fiber isn’t available in your area, simply fill out the Interest Form. PEAK uses clusters of Interest to determine future fiber builds.
What is Total Home Managed Wi-Fi and what are the benefits?
The services available vary greatly by area. Please call us to find out Wi-Fi options are available to you!
Call 541-754-7325
Does PEAK have contracts?
PEAK Internet does not require residential customers to sign long term contracts.
Can I save money with PEAK Internet vs. Cable or Satellite?
One of the key differences between PEAK Internet and both cable and satellite providers, is that all of PEAK Internet services include unlimited usage with no data caps. Also we don’t require our customers to bundle several services to get the best prices. We offer the best price possible on an ala carte’ basis. The only requirement is you have to subscribe to PEAK Internet for the other services to work.
What if I rent the residence I reside in instead of owning?
PEAK is always happy to work with your landlord or rental company. We do require that before we install our equipment that we have either written permission or a faxed letter of consent from the landlord or rental company.
What internet speeds are offered through PEAK?
At PEAK Internet we offer service through Fixed Wireless and Fiber connections at different reliable speeds. Follow the links below to view the different speed packages we offer:
Can I watch TV through PEAK Internet?
Yes, our live tv platform gives you all the same programming as a standard cable package, but runs on all your favorite devices such as smartphones, tablets, streaming media boxes, etc.
Do I need to be present for my internet installation?
Yes PEAK requires that a person 18 or older be present during the time of installation. If a contract is being signed then we want the account holder to be present.
How long does an installation take?
An installation will take approximately two hours, please be sure to either have yourself or an approved person on your account present during the installation. If you are interested in receiving service with PEAK Internet please call us at 541-754-7325 or visit either of the links below to get started.
How does fiber connect to my home?
Fiber is connected to a customer’s home via a piece of equipment called and ONT. The ONT is either installed on the outside of the house or in an easily accessible part of the home, such as the garage.
What if I already have an existing service in my home?
Some customers already have PEAK Internet Fixed Wireless Service when we build fiber into an area. These customers can easily convert from fixed wireless to PEAK Fiber.
How much does installation cost for Fixed Wireless?
Fixed wireless installation cost depends on the type of package you go with. With the agreement of a 2 year contract we only charge you our equipment deposit of $99.00 which would be included on your first bill. With a contractless installation we still charge the equipment deposit of $99.00 but we would also include an installation fee of $99.00, both charges would show up on your first billing. Installation costs and service costs are clearly laid out on the fixed wireless section of our website.
How much does installation cost for Fiber?
PEAK Internet’s base fee for fiber installation is $250 for up to 250 ft of aerial construction. Homes with longer drops or that require underground construction will be given an individual proposal for actual installation costs.
How do I connect to my Wi-Fi?
Connecting to Wi-Fi can depend on the type of device you are using. Most devices have either a setting or preference tab where the WI-FI settings for your device are located. From here you can scan for available networks. Once you have located your network name the device will then prompt you to enter either a WPA key or a passcode. If this is the first time you are using your new connection a network name and passcode is provided to you. If you do need further assistance our tech support is available 24/7 at 541-754-7325.
What is a Fiberhood?
A Fiberhood is an area that PEAK has decided to build fiber to. Fiberhoods are established in two ways; the first is developed by PEAK Management to help achieve organizational goals. The second is developed when several prospective customers in an area all submit interest in receiving PEAK Fiber. When there are enough of these interests submitted PEAK will create a Fiberhood and begin the process of building fiber to the area.
How can I check on the status of my Fiberhood?
To check on the status of your Fiberhood, you can go to Fiberhood Watch page and select your Fiberhood to see the status and map, or enter your address to find your Fiberhood.
How can I join Fiberhood Watch?
Joining the fiberhood watch is a great opportunity to see the status of any pending PEAK fiber builds in your area. By submitting interest in our fiber service you can then see the status of any fiber builds in your area. You can also check to see how many of your neighbors have submitted their interest for PEAK fiber. You can submit an interest form here.
Do I need to pay money upfront?
We do not request for you to pay upfront for services, our Customer Service Representatives will work with you to set up a payment plan, you are able to look at via your SmartHub account.
What streaming services are allowed with PEAK Fiber?
With your high speed and reliable connection with PEAK Internet you can access any streaming service of your choice with a compatible device.
Do you have a price guarantee?
All of PEAK’s residential services are offered on a Month-to-Month basis and as such prices are subject to change. However, PEAK has never had a rate increase on our Residential Internet Packages.
Does PEAK engage in the practice of “Speed Throttling”?
No PEAK will never throttle or cap the data transmission of your connection. If your connection appears to not be working as it should call our tech support 24/7 at 541-754-7325.
Are the Internet packages an accurate representation of the upload and download speeds?
Yes, PEAK will make sure to meet or exceed the marketed speeds that you are subscribed to. With our fixed wireless service PEAK will not complete a new installation unless our installer determines that the connection is stable and meets the specifications that we set.
Do I need special equipment to get streaming services?
PEAK Internet provides fast, reliable services to your residence or business, to access streaming services you can connect a device (ex: Apple TV, Amazon Fire) or Smart TV to your PEAK Internet connection.
Can I get your fiber or fixed wireless services in my apartment or condominium?
Yes, PEAK is happy to provide internet options at your apartment or condominium as long as the landlord or rental company allows us to install our equipment. Is it up to the resident to get permission.
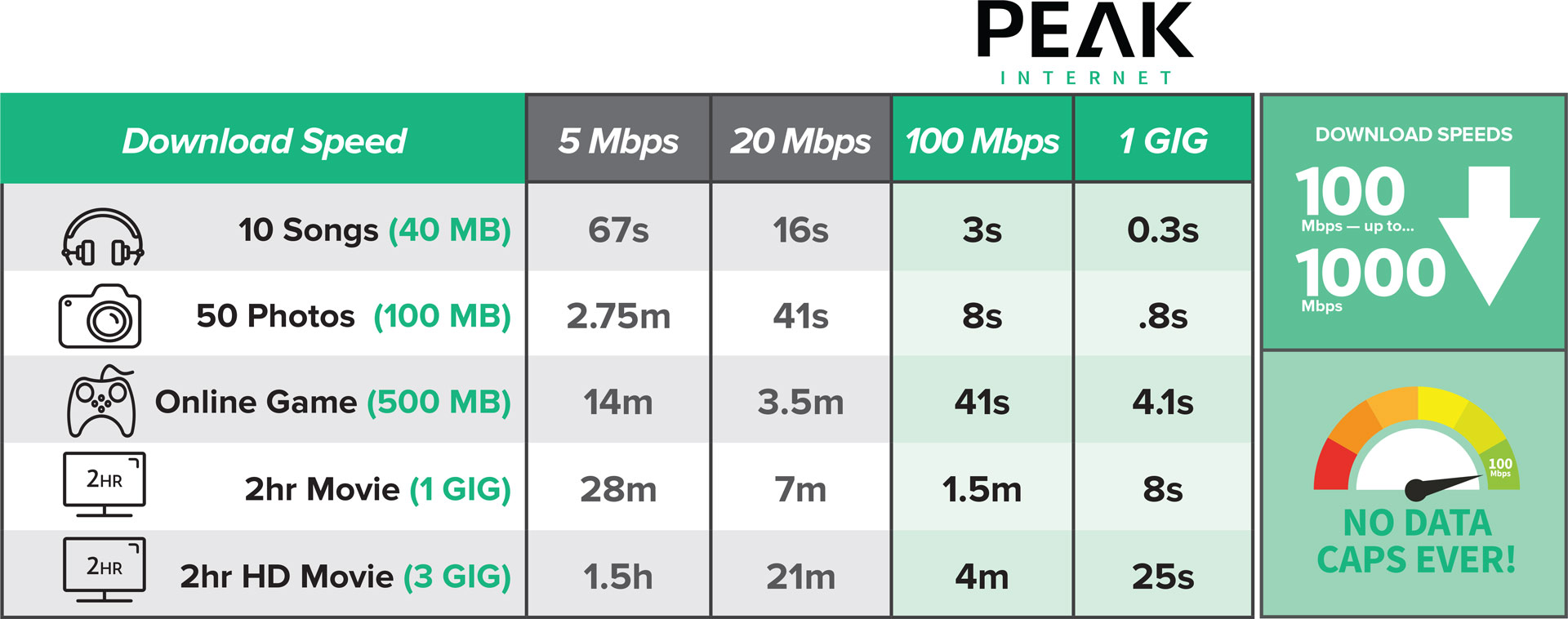
How fast is 100 Mbps or 1,000 Mbps?
What is the difference between download and upload speeds?
This is a very common question, It is important to know that when speaking of internet speeds Internet Service Providers talk in terms of Megabits per second (Mbps). When comparing different providers pay close attention not only to the download speed (usually the first number), but also the upload speed (usually the second number). Both of these numbers are important and will play an important role in how “good” the Internet Service is you will receive. A download speed takes into account the speed in which you receive data from the internet. For example receiving an email or downloading a movie. Upload speed takes into account the speed in which you send data to the internet. For example, sending an email to your friends or uploading a picture to facebook.
Is telemedicine or virtual medicine made available through PEAK Fiber?
One of the growing trends in the medical industry is Telemedicine. PEAK Fiber offers a very robust connection that will allow customers to utilize this new technology without any issues.
Are there any discounts available for your service(s)?
PEAK has made a decision to offer all of our services at our best price points and not to require bundling to get the best prices. One of the largest complaints about Internet Service Providers in general is that in order to get the best prices they require customers to bundle products together, and many times those customers don’t want or need the additional products. PEAK does not do that! Pick the products that you want and know that you are getting our best price. The only product that we do require that customers buy is Internet Connectivity, as all of our services are based on that product.
Do I need a modem or router for my new PEAK fiber service?
PEAK will provide all the equipment needed to be able to connect your devices to our services.
What is LOS or line of sight?
Line of sight is very important when speaking about our Fixed Wireless product. It is critical that the dish that we install on your home has a clear line of sight to one of our towers. If a tree, a hill, or another building is blocking any part of that view the service will be greatly affected or might not work all together.
What is an ISP?
ISP stands for Internet Service Provider.
Where can PEAK provide internet service?
PEAK provides internet services from just south of Salem to just north of Eugene, and just east of Corvallis to just east of Sweet Home. We utilize two different technologies to serve this large area, Fiber and Fixed Wireless. Fiber is not available in all areas, and customers wanting to see Fiber availability should check out our website for more information. Fixed Wireless while covering a much larger area does have line of sight restrictions, so there may be homes that we can not serve if a clear line of sight can not be established from the home to one of our towers.
Is my credit/debit card information safe once I hand it over to PEAK Internet?
Yes. We take the security of our customers’ private information very seriously. Cards that are used for automatic bill pay in our SmartHub system are in a completely secure system, and periodic security checks are done to ensure the integrity of that system.
Can I get a landline with my PEAK Internet service?
It depends on the service that you are subscribed to. For our fixed wireless service we do not offer a landline option at this time. If you are a PEAK fiber subscriber then yes we do offer a VOIP landline option with all the features you would expect like a voicemail portal, caller ID and more.
Can I continue to use my existing landline number if I switch to PEAK’s phone service?
Yes, PEAK fiber subscribers that choose our landline option will be able to keep their Centurylink or other carriers number if they choose. We would also be happy to provide you with a new phone number if you choose.
What phone features are included with my PEAK landline service?
PEAK’s Voice Services include the following, Local Calling, Long Distance (*Continental U.S. only), Standard 8hr UPS Battery, Voicemail, Caller ID with Name, Call Waiting, Call Forwarding, 3-way calling, and many more. For a full list of features please contact PEAK’s Customer Service Team at 541-754-7325.
Is my PEAK landline service registered with E911?
Yes.
Fiber
If you are having connectivity issues with your fiber connection, please call customer service at this time. 541-754-PEAK (7325)
Fixed Wireless
If you think that your Fixed Wireless connection has failed, the first course of action is to perform a power cycle of your home network, to rule out any local issues. Power cycling in this manner is better, as it allows any connection that previously existed to completely drop, and takes into account the time it may take for a new connection to be created before you attempt to connect.
- Unplug the power cords to your POE and your router if you have one.
- Wait a full three minutes, and then plug in your POE back into power.
- Wait a full two minutes, and then plug in your router.
- Wait thirty seconds and then check your connection for connectivity.
If this basic troubleshooting does not resolve your problem, try another device or power cycle the device you are using to try and connect, or give us a call!
Dial-Up
Dial-up is an olderservice that is primarily used as a backup connection, or where no other options are available as the internet really isn’t developed for dial-up anymore.
- Restart the computer.
- Check the line for dial-tone, remove any splitters that may be between the computer and the jack.
- Confirm that the line from the modem to the wall is in good condition and shorter than six feet. Ensure that both ends are not corroded, and clip firmly into the back of the computer and the wall jack. If your dial-up modem has two ports, ensure you are selecting the one for the modem.
If you find yourself frequently disconnecting from dial-up, disable any Call Waiting features you may have on the line, as these will interrupt your session.
If you need additional help troubleshooting, give us a call!
Wi-Fi Signal Interference
So many of our favorite devices require solid wireless connectivity to be their best, but not all of the corners of your home are wireless-friendly.
Diagnosing Wireless Interference
Wireless interference can have many symptoms. Maybe your audio is choppy, delayed or cutting out during your web meetings. Perhaps you can’t stream videos from the den, or you’ve noticed that your phone can’t connect to the wireless when you’re in the kitchen or the Roku in the kids’ room takes forever to load channels.
These are things that may indicate that wireless interference is affecting YOU. There are a number of complicated and time-consuming solutions that you could try to resolve the issue. You could wire your entire home for ethernet connectivity, or install expensive range extenders… OR you could let us solve the problem for you.
Our Total Home Premium managed wireless solution is installed by professionals who can heat-map your entire home and determine the best placements to access points and customize your in-home personalized wireless solution.
Click here to see videos about what you can do with the PEAKZone App.